
We're excited to tell you about Nuclei Templates release v10.0.0! This new version includes newly added Azure Config Review templates. In this blog post, we'll discuss automating azure cloud misconfiguration review, creating custom Azure checks, and sharing results on the PDCP Cloud for review.
Following our last release on AWS Cloud Security Config Review and Kubernetes Cluster Security, we decided to expand our coverage to include Azure as well.
Azure is well-known for its powerful features and vast configuration options, which can be challenging to manage. To make securing Azure environments easier, we’ve created our security checks in a simple YAML format, allowing for easier management and review of configurations
For those particularly interested in using the Azure Config templates, feel free to skip to the end of the blog
Azure Cloud Config Security Review
Often simply referred to as Azure Security Audit, this process is crucial for assessing the security measures in place within your Azure environments. It involves a detailed review of configurations, policies, and setups to ensure they align with security best practices and compliance requirements
Some key activities in an Azure Cloud Config Security Review typically include:
- Identity and Access Management Review: This involves verifying that proper roles are assigned and that Multi-Factor Authentication (MFA) is enabled, especially for privileged users.
- Resource Configuration and Management: Checking resource locks, and ensuring that logging for resource deletion and updates is enabled to trace critical changes.
- Network Security Configuration: This includes ensuring that network security groups (NSGs) are properly set up to restrict unnecessary external access and internal traffic to minimize the risk of breaches.
- Compliance and Regulatory Adherence: Verifying that all Azure services comply with industry-specific regulations, such as HIPAA for healthcare or PCI DSS for payment processing industries.
- Security Best Practices and Policies: Ensuring that security controls like encryption for storage accounts and databases are enforced, and that only secure protocols are used for communication.
We realize that reviewing Azure cloud configurations can feel overwhelmingly complex, often more challenging than it needs to be. That’s why we’ve chosen to streamline the process by creating security checks for Azure using the straightforward YAML format used by Nuclei. These templates perform all essential checks, encompassing configurations, logging, compliance, and best practices. By leveraging these templates, we can effortlessly produce a comprehensive report on our cloud platform, detailed with remediation steps. This simplified approach makes the review process much smoother for both companies and penetration testers.
Before we launch into the scanning process, let’s discuss a bit about the Azure code review nuclei-templates. These have been crafted using code protocols to help a thorough review of Azure cloud configurations.
What are Code Protocol Templates?
Nuclei empowers users to execute external code on the host operating system, granting security researchers, pentesters, and developers the flexibility to expand its capabilities beyond standard protocol-based testing. This functionality enables interaction with the underlying OS, facilitating the execution of custom scripts or commands for a diverse array of tasks including system configurations, file operations, and network interactions. Such control and adaptability empower users to customize their security testing workflows to meet precise needs. Explore the Code protocol templates in our documentation for more details.
Because code templates can execute commands on hosts, users must first sign the template using their keys, and these are not included in default scans. To use these templates, you need to sign them using the-signflag. After signing, you can run the templates by providing the-codeflag.
In the example below, you'll notice that we can easily run an az command directly from the template. However, unlike other templates that execute on target hosts, this one will run the command on our own host.
yaml
1id: azure-env
2info:
3 name: Azure Environment Validation
4 author: princechaddha
5 severity: info
6 description: |
7 Checks if Azure CLI is set up and all necessary tools are installed on the environment.
8 reference:
9 - https://portal.azure.com/
10 metadata:
11 max-request: 2
12 tags: cloud,devops,microsoft,azure,azure-cloud-config
13
14self-contained: true
15code:
16 - engine:
17 - sh
18 - bash
19 source: |
20 az account show
21
22 matchers:
23 - type: word
24 words:
25 - '"homeTenantId":'
26
27 extractors:
28 - type: json
29 name: environmentname
30 json:
31 - '.environmentName'
32 internal: true
33
34 - type: dsl
35 dsl:
36 - '"Azure CLI is properly configured for environment \"" + environmentname + "\"."'Example #1:
In this example, we will create a template that identifies privileged Azure users who do not have Multi-Factor Authentication (MFA) enabled, a common oversight that can lead to security breaches.
- We've set
self-contained: truebecause this Nuclei template operates independently of any specific host, using local Azure configurations to fetch and analyze user data. - The first code block starts by specifying the engine we wish to use for executing the command, followed by the command itself in the
sourcesection. This block includes an extractor that extracts the list of user principal names and stores them in theuserListarray. - After defining the initial code block, we introduce a flow, a recently added feature that controls the execution sequence of the template. Initially, we execute
code(1)to fetch the user data. This is followed by iterating over each user in theuserListusing a for loop, setting the current user as theuserPrincipalName, and then executing the second code block. - The second code block runs the Azure CLI command
az role assignment list --include-classic-administrators true --assignee "$userPrincipalName" --query '[].{roleDefinitionName:roleDefinitionName}' --output json. This command checks if the user has roles like Owner, Contributor, or Administrator assigned to them. - Using matchers, we check if the role definitions returned include any of the specified roles, indicating privileged access.
- Finally, the last extractor outputs the user names of those privileged users who do not have MFA enabled, providing critical information for remediation.
yaml
1id: azure-mfa-not-enabled-privileged-users
2
3info:
4 name: Azure MFA Not Enabled for All Privileged Users
5 author: princechaddha
6 severity: high
7 description: |
8 Ensure that Multi-Factor Authentication (MFA) is enabled for all user credentials that have write access to the cloud resources within your Microsoft Azure account. Multi-Factor Authentication is a simple, yet efficient method of verifying your Azure user identity by requiring an authentication code generated by a virtual or hardware device, also known as passcode, used in addition to your usual access credentials such as user name and password.
9 impact: |
10 Without MFA enabled for privileged users, there is an increased risk of unauthorized access which can lead to potential breaches and significant impact on cloud resources and data security.
11 remediation: |
12 Configure Multi-Factor Authentication for all privileged Azure user accounts to enhance security measures and prevent unauthorized access.
13 reference:
14 - https://docs.microsoft.com/en-us/azure/active-directory/authentication/concept-mfa-howitworks
15 tags: cloud,devops,azure,microsoft,multi-factor-authentication,azure-cloud-config
16
17flow: |
18 code(1)
19 for (let User of iterate(template.userList)) {
20 set("userPrincipalName", User)
21 code(2)
22 }
23
24self-contained: true
25code:
26 - engine:
27 - sh
28 - bash
29 source: |
30 az ad user list --query '[].{userPrincipalName:userPrincipalName}' --output json
31
32 extractors:
33 - type: json
34 name: userList
35 internal: true
36 json:
37 - '.[].userPrincipalName'
38
39 - engine:
40 - sh
41 - bash
42 source: |
43 az role assignment list --include-classic-administrators true --assignee "$userPrincipalName" --query '[].{roleDefinitionName:roleDefinitionName}' --output json
44
45 matchers-condition: and
46 matchers:
47 - type: word
48 words:
49 - 'Owner'
50 - 'Contributor'
51 - 'Administrator'
52
53 extractors:
54 - type: dsl
55 dsl:
56 - '"userPrincipalName + " is a privileged user without MFA enabled"'Example #2:
This template checks Azure Key Vaults to identify SSL certificates that are missing auto-renewal, helping prevent outages and security risks from expired certificates.
yaml
1id: azure-keyvault-ssl-autorenewal-missing
2info:
3 name: Missing SSL Certificate Auto-Renewal in Azure Key Vaults
4 author: princechaddha
5 severity: high
6 description: |
7 Microsoft Azure Key Vault service can renew your SSL certificates automatically to prevent application or service outages, credential leaks, or process violations that can disrupt your business. Ensure that your SSL certificates in Azure Key Vaults are set to auto-renew.
8 impact: |
9 Not enabling auto-renewal for SSL certificates can lead to expired certificates, potentially causing outages and security risks.
10 remediation: |
11 Configure SSL certificates in Azure Key Vaults to automatically renew by setting the correct policies in the Azure portal or through Azure CLI.
12 reference:
13 - https://docs.microsoft.com/en-us/azure/key-vault/certificates/how-to-renew-certificate
14 tags: cloud,devops,azure,microsoft,keyvault,azure-cloud-config
15
16flow: |
17 code(1);
18 for (let KeyVaultName of iterate(template.keyVaultNames)) {
19 set("vaultName", KeyVaultName)
20 code(2);
21 for (let CertificateId of iterate(template.certificateIds)) {
22 set("certificateId", CertificateId)
23 code(3)
24 }
25 }
26
27self-contained: true
28code:
29 - engine:
30 - sh
31 - bash
32 source: |
33 az keyvault list --query '[*].name' --output json
34
35 extractors:
36 - type: json
37 name: keyVaultNames
38 internal: true
39 json:
40 - '.[]'
41
42 - engine:
43 - sh
44 - bash
45 source: |
46 az keyvault certificate list --vault-name $vaultName --query '[?(attributes.enabled==`true`)].id' --output json
47
48 extractors:
49 - type: json
50 name: certificateIds
51 internal: true
52 json:
53 - '.[]'
54
55 - engine:
56 - sh
57 - bash
58 source: |
59 az keyvault certificate show --id $certificateId --query 'policy.lifetimeActions[*].action.actionType' --output json
60
61 matchers:
62 - type: word
63 words:
64 - '"EmailContacts"'
65
66 extractors:
67 - type: dsl
68 dsl:
69 - 'vaultName + " SSL certificate " + certificateId + " does not have auto-renewal enabled"'Example #3:
This template checks if remote debugging is enabled for Azure App Service web applications, which poses a security risk by potentially exposing the application to unauthorized access.
yaml
1id: azure-appservice-remote-debugging-enabled
2info:
3 name: Azure App Service Remote Debugging Enabled
4 author: princechaddha
5 severity: high
6 description: |
7 Ensure that your Azure App Services web applications have remote debugging disabled in order to enhance security and protect the applications from unauthorized access. Remote Debugging feature is available for web applications (e.g. ASP.NET, ASP.NET Core, Node.js, Python).
8 impact: |
9 Enabling remote debugging can expose web applications to unauthorized access and potential security vulnerabilities.
10 remediation: |
11 Disable remote debugging for Azure App Services web applications through the Azure portal or using Azure CLI commands to enhance application security.
12 reference:
13 - https://docs.microsoft.com/en-us/azure/app-service/troubleshoot-remote-debug
14 tags: cloud,devops,azure,microsoft,appservice,azure-cloud-config
15
16flow: |
17 code(1);
18 for (let WebAppData of iterate(template.webAppList)) {
19 set("ids", WebAppData);
20 code(2);
21 }
22
23self-contained: true
24code:
25 - engine:
26 - sh
27 - bash
28 source: |
29 az webapp list --query '[*].{id:id}' --output json
30
31 extractors:
32 - type: json
33 name: webAppList
34 internal: true
35 json:
36 - '.[].[]'
37
38 - engine:
39 - sh
40 - bash
41 source: |
42 az webapp config show --ids $ids --query 'remoteDebuggingEnabled' --output json
43
44 matchers:
45 - type: word
46 words:
47 - "true"
48
49 extractors:
50 - type: dsl
51 dsl:
52 - 'id + " has remote debugging enabled."'Check out all the other azure templates by visiting the Nuclei Templates GitHub repository.
Custom Templates for Specific Use Cases
Custom Azure security checks allow security teams, pentesters, and DevOps professionals to address unique security concerns and operational practices within their Azure environments. Here are a few scenarios where creating custom Azure Nuclei templates might be particularly beneficial:
- Custom Resource Checks: For organizations that use specialized resources in Azure, custom templates can ensure these resources adhere to security best practices. For example, a template might check if certain Azure Function Apps have proper diagnostic settings enabled or if Azure App Services have remote debugging disabled.
- Specific Compliance Audits: Different industries have specific regulatory requirements. Custom templates can help enforce compliance through continuous monitoring. For instance, a template could verify that all Azure SQL databases have Transparent Data Encryption (TDE) enabled to comply with industry security standards.
- Service-Specific Policies: Azure services like Azure Kubernetes Service (AKS) or Azure Virtual Machines may have unique security policies based on their roles and exposure. Custom templates can help ensure that each service adheres to its specific security policies, such as enforcing disk encryption on all VMs or checking that AKS clusters use the latest Kubernetes version.
- Integration with CI/CD Pipelines: Custom templates can be integrated into CI/CD pipelines to automatically check for security issues before new deployments are rolled out. For example, a template might scan new Azure Resource Manager (ARM) templates for misconfigurations or check that new services are deployed with the necessary security controls in place.
- Advanced Network Security Testing: While basic checks for network security are vital, custom templates can perform more sophisticated testing to ensure that the implemented network controls effectively protect different parts of the Azure environment. This might involve detailed checks on Network Security Groups (NSGs) or ensuring that all public-facing endpoints are protected by Azure Firewalls.
- Performance and Resource Optimization: Beyond security, custom templates can also help optimize the performance and resource usage of Azure services. For instance, a template might identify over-provisioned resources or services not using Azure Advisor recommendations effectively.
Running Azure Security Templates
To use these templates, ensure your environment is set up correctly. You need to install the Azure CLI and configure its contexts or specific access permissions.
In Nuclei-Templates, we've introduced the concept of profiles, which allow users to run a specific set of templates tailored for a particular use case. For Azure Cloud Config security reviews, we have a profile named azure-cloud-config.
Once the environment is properly configured, users can execute the following command to ensure everything is set up correctly before running the profile:
CLI
1pwnmachine@PD azure % nuclei -id azure-env -code
2
3 __ _
4 ____ __ _______/ /__ (_)
5 / __ \/ / / / ___/ / _ \/ /
6 / / / / /_/ / /__/ / __/ /
7/_/ /_/\__,_/\___/_/\___/_/ v3.3.2
8
9 projectdiscovery.io
10
11[INF] Current nuclei version: v3.3.2 (latest)
12[INF] Current nuclei-templates version: v9.10.0 (latest)
13[WRN] Scan results upload to cloud is disabled.
14[INF] New templates added in latest release: 59
15[INF] Templates loaded for current scan: 1
16[INF] Executing 1 signed templates from triage
17
18[azure-env] [code] [info] ["Azure CLI is properly configured for environment "AzureCloud"."]If the template matches, this indicates that the environment has all the necessary tools installed and the CLI is set up.
Users can also select the subscription they want to scan using the following command if they have multiple subscriptions before running the templates:
az account set --subscription <subscription-id>
Uploading Results to ProjectDiscovery Cloud Platform
To upload results to the cloud, you need to obtain an authentication token. Here are the steps to follow:
- Go to PDCP Cloud and log in to your account.
- Click on your profile picture in the top-right corner and select API key.
- Copy your API key, and in your terminal, type
nuclei -auth <your-api-key>.
Now you're all set to run the templates!
nuclei -profile azure-cloud-config -cloud-upload

Now that we have a lot of findings, it would be very convenient to view these on the Cloud. Simply log into PDCP Cloud, and you will find a scan created with the results.
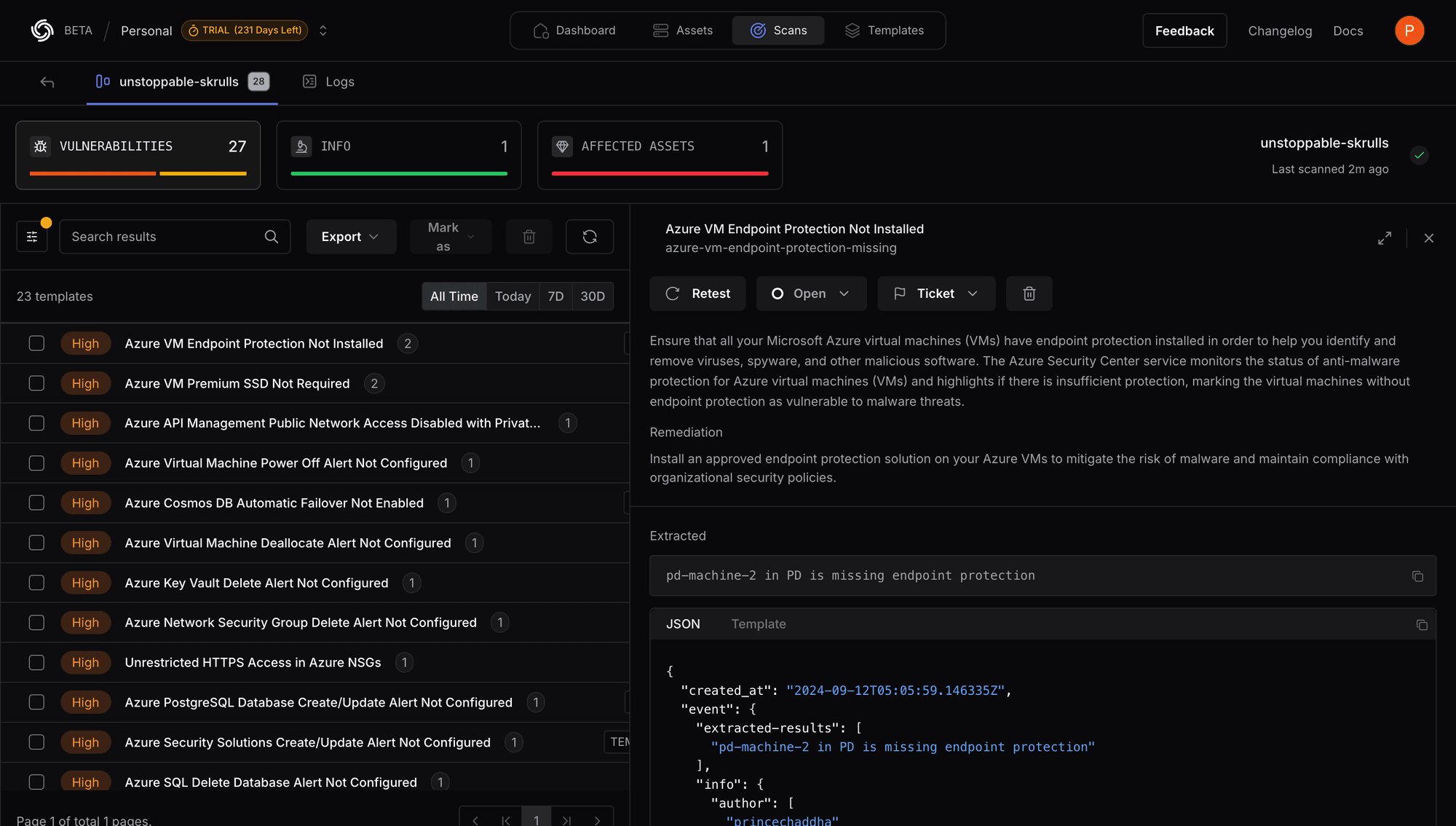
We have added 192 templates categorized by services. We invite the community to share their feedback. We anticipate this number will grow as the security community continues to contribute and collaborate.
Conclusion
The Nuclei templates for Azure provide significant creativity and flexibility, enabling users to craft checks that cater to their specific workflow and environment. This approach not only helps in identifying and resolving security misconfigurations but also facilitates monitoring of their overall Azure environment.
You can also join our Discord server. It's a great place to connect with fellow contributors and stay updated with the latest developments. Thank you, once again!
By leveraging Nuclei and actively engaging with the open-source community, or by becoming a part of the ProjectDiscovery Cloud Platform, companies can enhance their security measures, proactively address emerging threats, and establish a more secure digital landscape. Security represents a shared endeavor, and by collaborating, we can consistently adapt and confront the ever-evolving challenges posed by cyber threats.